PRAPD: A novel received signal strength–based approach for practical rogue access point detection - Wenjia Wu, Xiaolin Gu, Kai Dong, Xiaomin Shi, Ming Yang, 2018
![Unsecured Rogue Access Point Allows Anyone to Connect to the Network [17] | Download Scientific Diagram Unsecured Rogue Access Point Allows Anyone to Connect to the Network [17] | Download Scientific Diagram](https://www.researchgate.net/publication/276230435/figure/fig3/AS:668979894951955@1536508644638/Unsecured-Rogue-Access-Point-Allows-Anyone-to-Connect-to-the-Network-17.jpg)
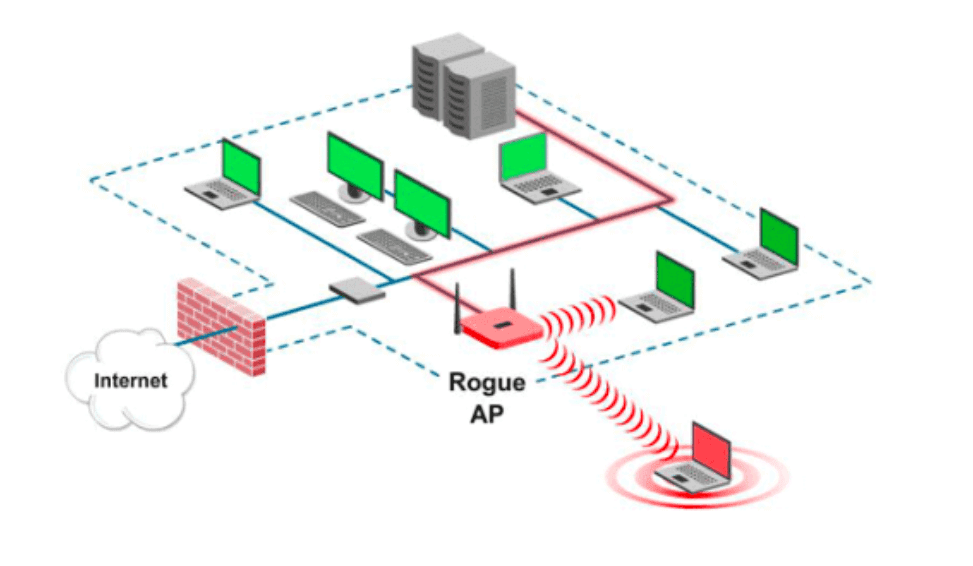
Unsecured Rogue Access Point Allows Anyone to Connect to the Network [17] | Download Scientific Diagram
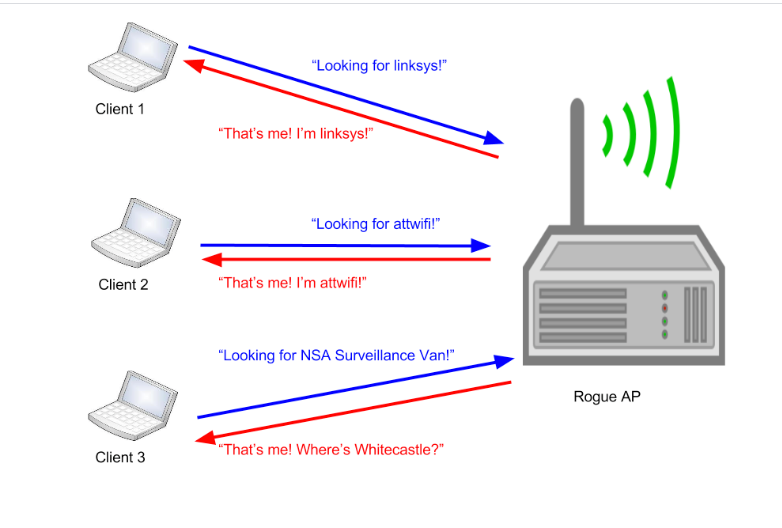
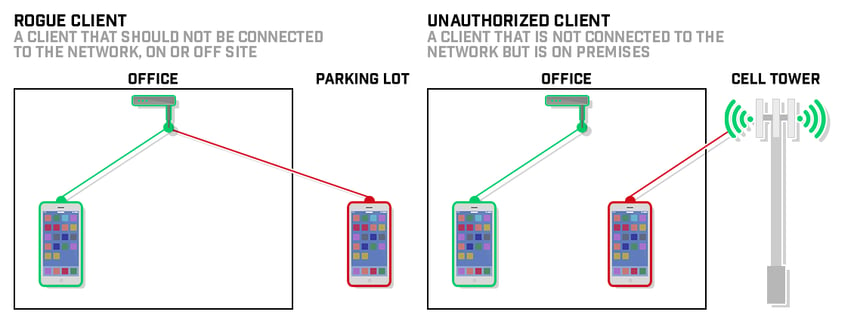
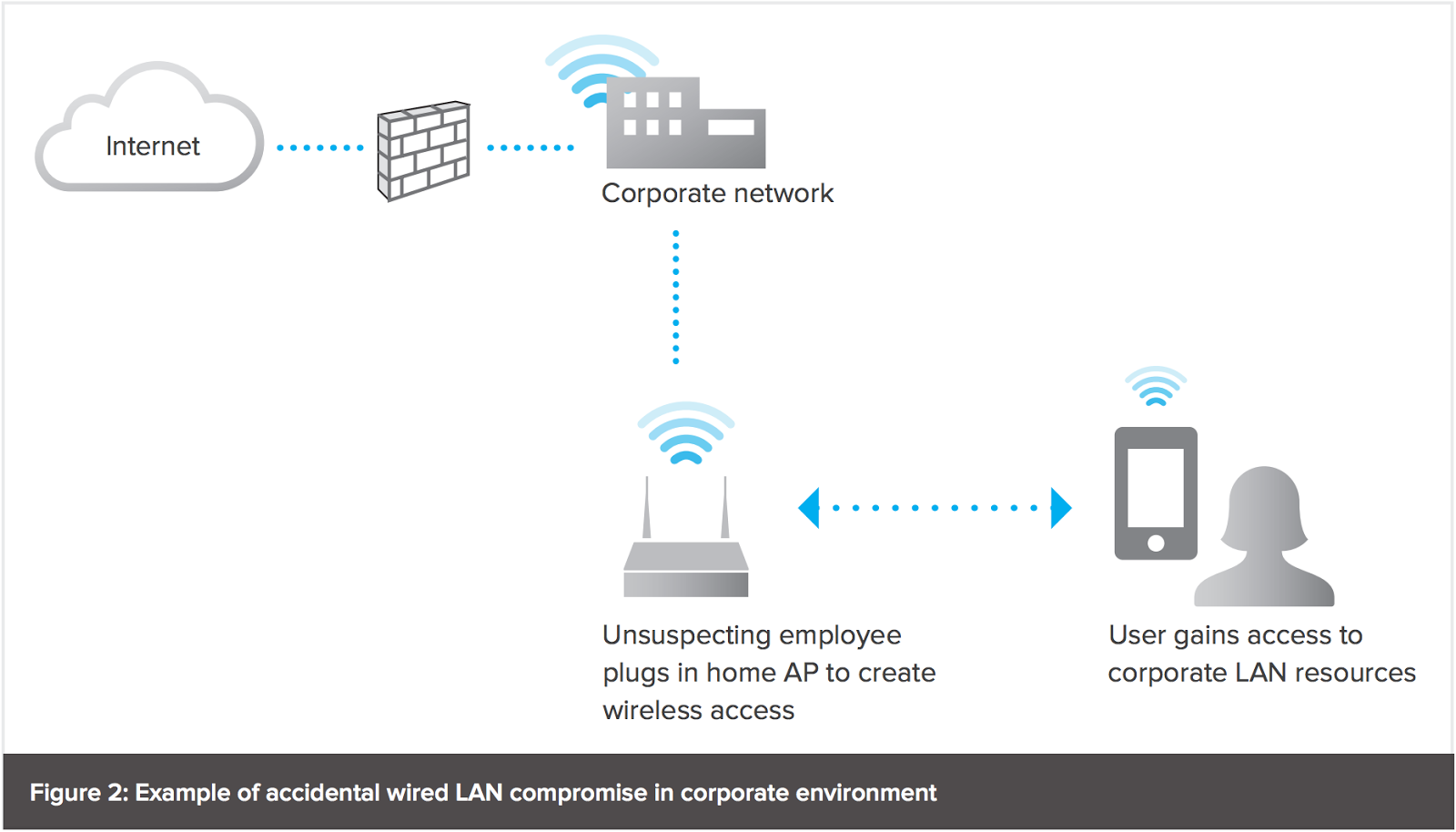
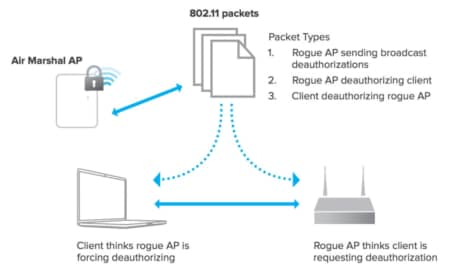
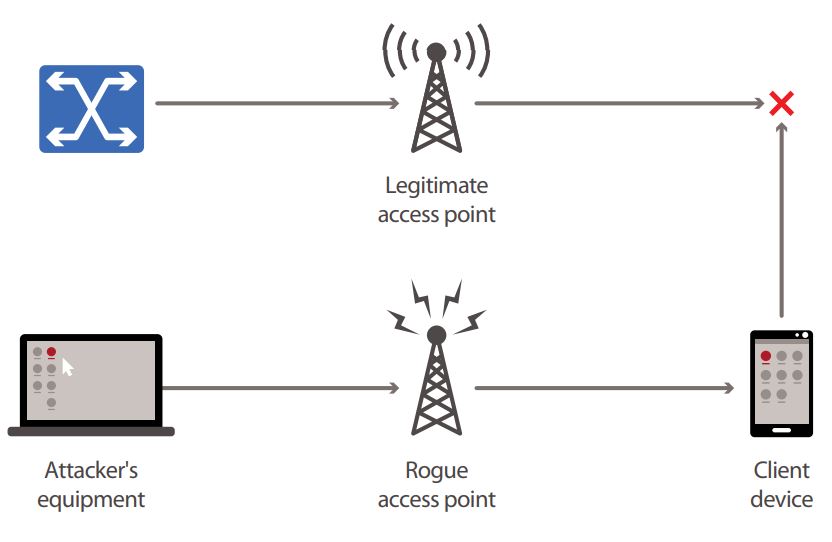
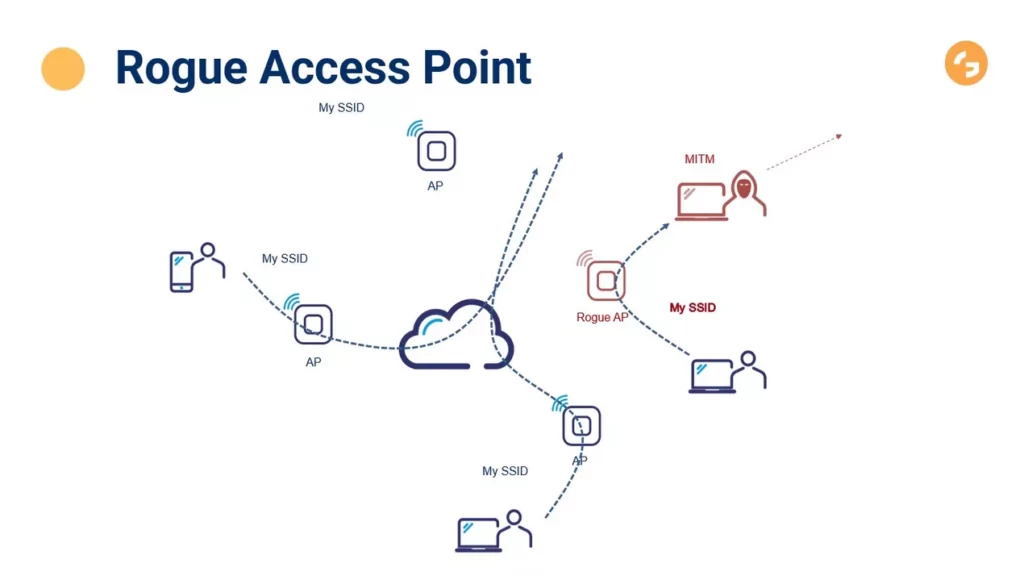
Modern Wireless Tradecraft Pt I — Basic Rogue AP Theory — Evil Twin and Karma Attacks | by Gabriel Ryan | Posts By SpecterOps Team Members

![PDF] A Flexible Framework for Rogue Access Point Detection | Semantic Scholar PDF] A Flexible Framework for Rogue Access Point Detection | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/5f7a2fec5198aa5b1f3c846b4db50aec4dff4e3b/29-Figure2.2-1.png)





![PDF] Rogue Access Point Detection System in Wireless LAN | Semantic Scholar PDF] Rogue Access Point Detection System in Wireless LAN | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/41a44df312f08ce3551a932335310d6e542e2fa7/4-Figure6-1.png)